If you’re one of the many business users who has not upgraded their computer to Windows 10, there are still resources to boost your experience. Here are 10 tips for getting the most out of the OS.

Windows 10 faced a controversial roll-out, with privacy concerns, bugs, and other issues plaguing many users. And as of August 2016, just 1% of business machines had upgraded to Windows 10, according to a study from Softchoice. Instead, 91% of the machines were operating with Windows 7—an 18% increase over the same period of time in 2015.
“It seems businesses don’t see an urgent need to move operating systems, so long as their cloud-based applications are still running fine on Windows 7,” Softchoice’s Microsoft director Craig McQueen wrote in a press release at the time. “In addition to the security benefits, I think once organizations grasp the user benefits—such as touch and Cortana—we will start to see a boost in adoption.”
While experts predict Windows 10 deployments will pick up this year, it’s important for those still using Windows 7 for business to get the most out of their machines. Here are 10 articles with Windows 7 tips that will help enterprise users operate the machines more effectively.
1. 10 ways to speed up Windows 7
While Windows 7 generally performs well, over time, the system can slow down and require some care to get it back up to speed. The OS also contains certain features that users can take advantage of to improve overall performance. Here, we outline 10 steps business users can take to enhance the performance of your Windows 7 system.
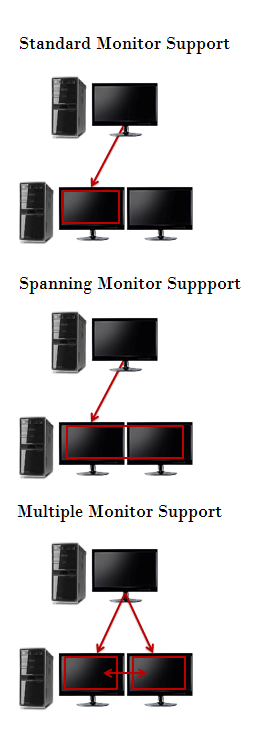
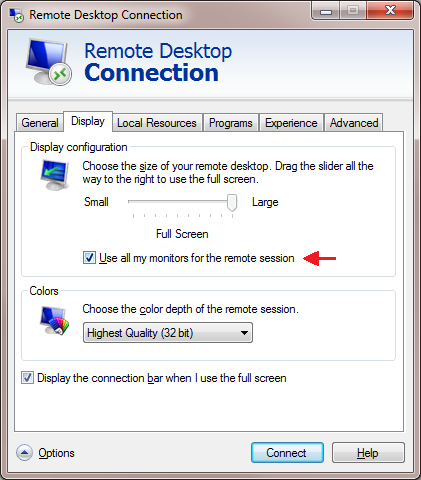
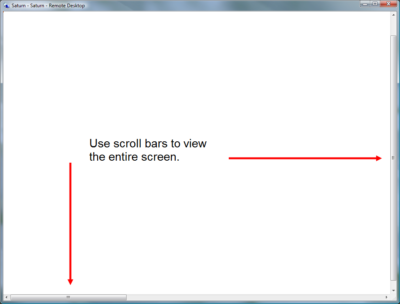
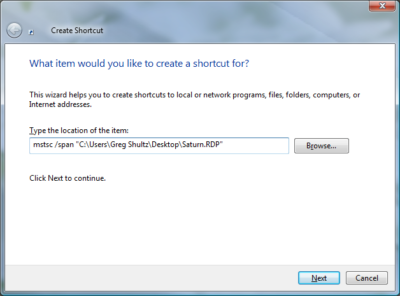
2. Use multiple monitors with Windows 7’s Remote Desktop Connection
Windows 7 allows users to connect to a remote computer and utilize the local system’s multiple monitors. Here is a step by step advice on how to configure and operate multiple monitors using Windows 7’s Remote Desktop Connection, as well as how to connect to and from Windows versions that do not support this feature.
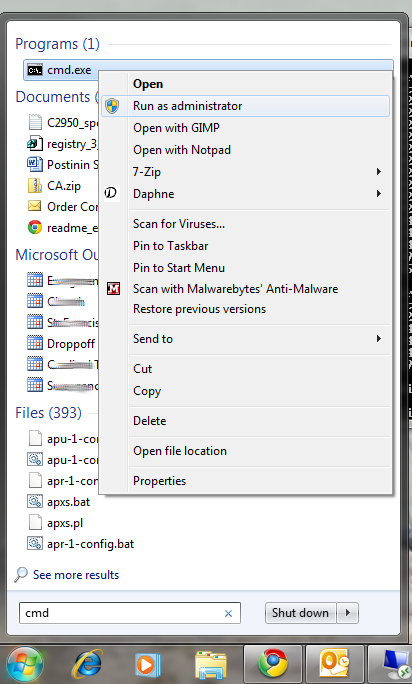
3. Quick Tips: Flush the ARP cache in Windows 7
The Address Resolution Protocol (ARP) cache is an important part of IP networking on any OS, as it links Ethernet addressing to hardware addressing. Newly mapped addresses are saved in an ARP cache, which is usually fine, but can sometimes cause issues with internet connections and web page loading times. Here, are the necessary steps to clear the ARP cache, and how to manage it going forward.
4. 10+ Windows 7 services you may not need
While every version of Windows includes a core set of system services, business users can disable some that are not necessary in order to improve performance and security. In this article, we highlight 13 services that users can disable if they so choose on Windows 7 systems that will likely not have any impact on business operations, including IP Helper, offline files, and Network Access Protection.
5. 10 Windows 7 commands every administrator should know
IT staff who troubleshoot Windows 7 problems often have to dive into the command line. Here, are 10 fundamental Windows 7 commands that are useful for IT administrators, including System File Checker, File Signature Verification, and Driverquery.
6. Modifying the Windows 7 boot loader with the Boot Configuration Data Editor tool
In Windows Vista and later versions of Windows, the bootloader was moved from boot.ini to a utility called BCDEdit. This article walks users through how to modify the boot config data using this tool.
7. Change and customize Windows 7’s Logon screen wallpaper
Changing and customizing the Windows 7 Logon screen wallpaper is easy once you know the steps, as Microsoft built the ability to change the wallpaper right into the OS, as opposed to needing any third-party software. Here, we offer a tutorial on doing so.
8. Change the Processor Affinity setting in Windows 7 to gain a performance edge
Most applications have been designed for multi-core processors, and work with an OS to distribute their operations evenly across cores to enhance performance. However, you can sometimes achieve better overall performance from certain applications by configuring them to run on different processor cores, which Windows 7 allows via the Processor Affinity setting. In this article, we explain two ways to change the Processor Affinity setting in Windows 7.
9. Use Windows 7 Event Viewer to track down issues that cause slower boot times
Experiencing a slow Windows 7 boot time? You can use Windows 7’s Event View to investigate the source of the problem. The Event Viewer includes a category of event logs called Applications and Services Logs, which track key elements of the OS. Here, we explain how it is possible to find out how long it took to boot up your system every time, since the day Windows 7 was first installed, along with instances where boot time slowed down, all through these logs.
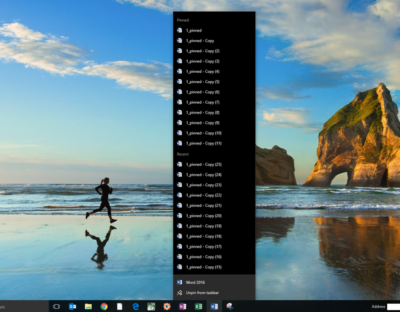
10. Tag your files for easier searches in Windows 7
This article, walks users through how to tag files to make them searchable via the Search filters built into Windows Explorer’s Search box in Windows 7. It’s possible to do this easily from many applications while saving a file. The ability to more easily find files is a boon for business users who want to enhance their productivity.
Have questions?
Get answers from Microsofts Cloud Solutions Partner!
Call us at: 856-745-9990 or visit: https://southjerseytechies.net/
South Jersey Techies, LL C is a full Managed Web and Technology Services Company providing IT Services, Website Design Services, Server Support, Network Consulting, Internet Phones, Cloud Solutions Provider and much more. Contact for More Information.
To read this article in its entirety click here.