Microsoft’s most direct shot at the MacBook yet
This slideshow requires JavaScript.
The one Surface product that fans have been clamoring over for years, a straight up Surface Laptop, is finally here. But, in taking design cues from both the Surface Pro and Surface Book lines, Microsoft has set lofty expectations for its first dedicated laptop device.
Priced at $999 (about £770, AU$1,330), the Surface Laptop clearly aims to chip at the MacBook and MacBook Air models that dominate college campuses practically worldwide. In fact, Microsoft claims that its cheaper (and larger) Surface Laptop can last far longer on a charge than Apple’s 12-inch MacBook: 14.5 hours.
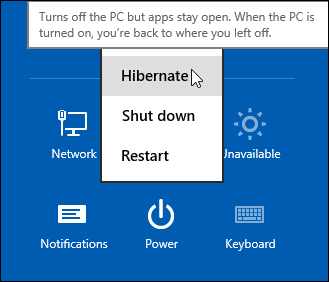
However, every Surface Laptop shipped will come with Windows 10 S installed, Microsoft’s new version of Windows 10 that only accepts app installs downloaded from the Windows Store.
With the ability to switch from Windows 10 S to the 100% open Windows 10 Pro for $49 if you miss the chance in 2017 for free, should you need an app outside of the Windows Store that badly (spoiler: you probably will).
Regardless, at that price, can Microsoft garner enough interest from college students (or more likely their parents), who are often already strapped from the cost of an education?

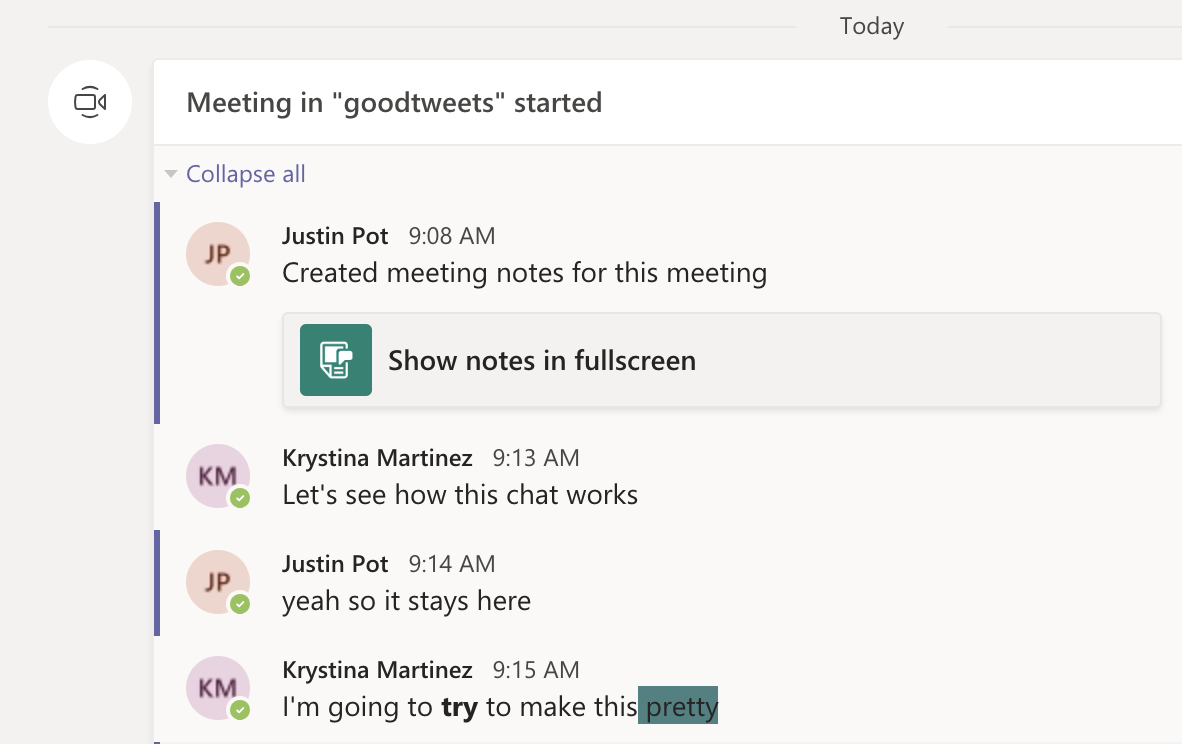
The Surface Laptop in traditional ‘Platinum’
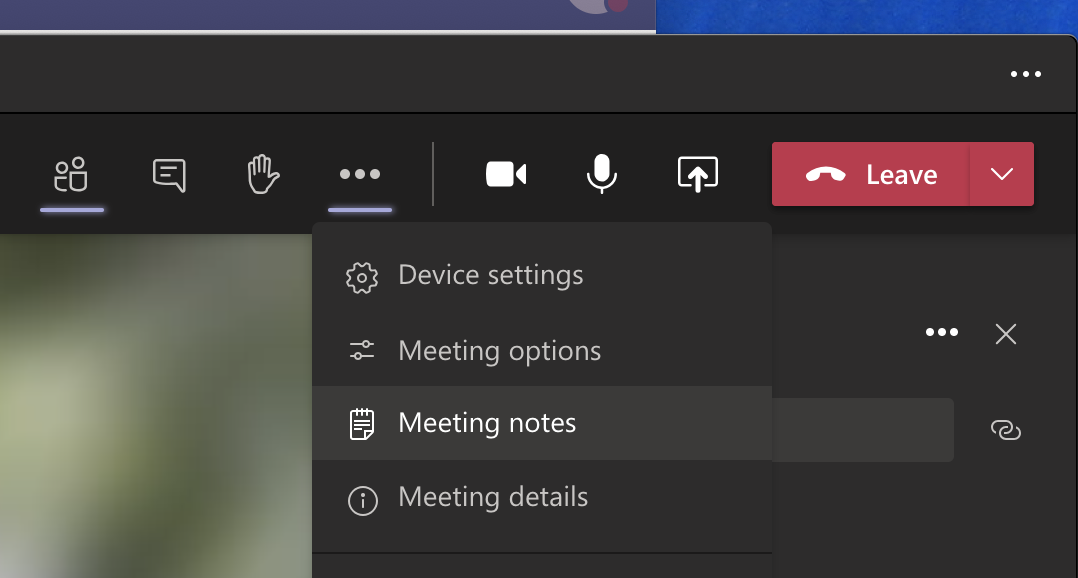
Design
Clearly, part of Microsoft’s plan is to lure those folks in with an incredibly gorgeous, and potentially trendsetting, design. The 13.5-inch Surface Laptop may very well be Microsoft’s most attractive computing product yet.
And, with four colors to choose from – Burgundy, Platinum, Cobalt Blue and Graphite Gold – there’s bound to be one that appeals to you.
A full aluminum lid and base wrap the laptop in much the same way it does a Surface Book, but ditches the aluminum in the keyboard deck for a Alcantara fabric that surrounds every plastic key and meets with the aluminum base in a seemingly airtight seal.
The fabric, according to Microsoft, is imported from Italy and laser cut to fit every Surface Laptop. Now, while many of the design elements are the same, the 13.5-inch (2,256 x 1,504) PixelSense touch display, the smooth glass-coated Precision touchpad, the chrome logo centered on the aluminum lid, we’re told that very few parts from previous parts are found within the Surface Laptop.
That much is obvious in the nature of the felt used for this keyboard deck compared against that which the Type Covers from Microsoft utilize. It’s smoother and more plush than those Type Covers, and we’re told it’s spill resistant.

The Surface Laptop’s keyboard deck is awfully comfortable
Plus, the additional height afforded by this traditional laptop design allowed Microsoft to equip the keyboard with 1.5mm of travel, and the difference in typing between that and the Surface Pro 4 is night and day. Finally, Microsoft devised a speaker system beneath the keyboard that radiates sound through the spaces between the keys and the keyboard deck.
The result isn’t much better audio than you’d find in a MacBook Air, perhaps a bit fuller, but at least it’s consistently in an uninterrupted position. Naturally, the audio gets a bit muffled when typing, but since the sound radiates throughout the laptop base, there isn’t a major loss in audio detail.
That leaves the side of the laptop base to house Microsoft’s proprietary power and docking port found on other Surface devices, as well as a USB 3.0 and Mini DisplayPort, not to mention an audio jack. If you’re already asking, “where’s the USB-C,” we’ve already been there.
Microsoft tells us that it intends for its own port to handle concerns of connectivity expansion via the Surface Connect port and its Surface Dock, while refraining from alienating customers that have yet to completely update to USB-C.
A fine explanation, but that doesn’t tell us why USB 3.0 and not USB 3.1 at least, as you’re missing out on some major data transfer speed improvements there.

Those strange strips of plastic on the base? They’re Wi-Fi antennae
Performance and battery life
Microsoft can pack the Surface Laptop with the latest Intel Core i5 or Core i7 processors (Kaby Lake), up to 512GB of PCIe solid-state storage (SSD) and as much as 16GB of RAM.
That’s a mighty powerful laptop on paper, likely stronger than either the MacBook Air or 12-inch MacBook, while rising above even the latest 13-inch MacBook Pro that still utilizes Skylake processors.
(The $999 model comes packing a 128GB SSD and 4GB of RAM with the Intel Core i5.)
As for how Microsoft fit that kind of power a laptop just 0.57 inches (14.48mm) thin, a brand new, proprietary vapor chamber cooling system helps a whole lot. The system changes the physical state of the heat as it’s taken in through the center of a fan vent in the rear of the laptop base and spits it out of the sides of that same vent.
While we obviously weren’t able to stress-test the Surface Laptop, we were able to test out how it feels to use. For starters, at just 2.76 pounds (1.25kg), this thing is super light, which is all the more impressive considering it’s a 13.5-inch, Gorilla Glass 3 touchscreen you’re looking at.

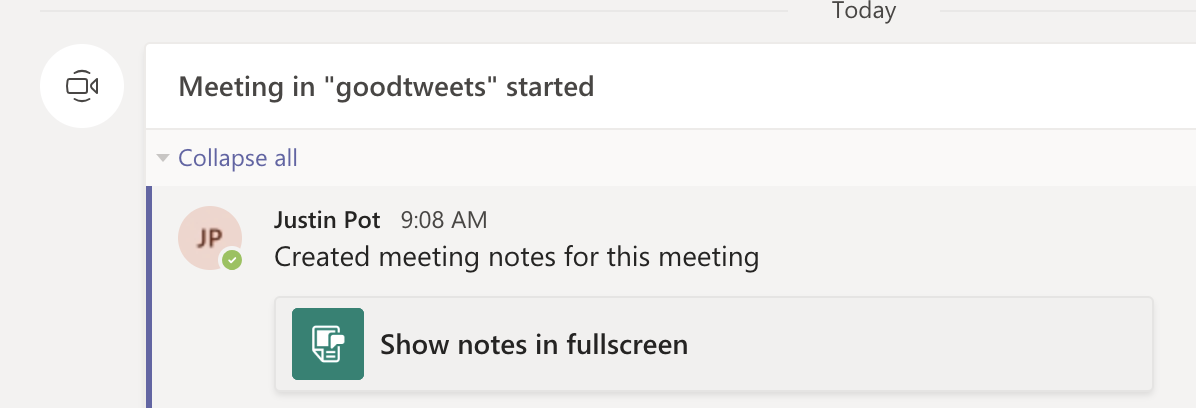
Note the Surface Connect dock port – Microsoft’s answer to USB-C
Microsoft chalks this up to, in part, the thinnest LCD touch module ever used in a laptop design. This, in turn, helps the lid to lift with just one finger. However, perhaps the hinge design needs refinement.
While you can open the display with just a finger, that slightness in the hinge is felt when the screen bounces with every tap of the touchscreen. It’s the very reason we question the inclusion of touchscreens in traditional laptops to begin with. Unfortunately, it seems Microsoft hasn’t found a better solution here.
That said, typing on the keyboard is the best time we’ve had doing such on a Surface product yet, and the portability of the whole thing is right there with Apple’s best.
As for battery life, Microsoft is, again, claiming 14.5 hours on a single charge. Microsoft later clarified for us that this number was achieved via local video playback with all radios but Wi-Fi disabled.
That testing environment sounds very similar to how TechRadar tests for battery life, so we might see battery life results in a full review fall much closer to this claim. If so, then Surface Laptop will be very tough to beat in longevity and be a potentially major driver for sales.

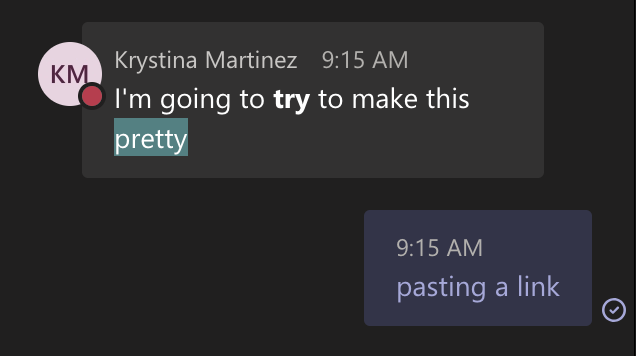
This is the Surface Laptop in Cobalt Blue
Early verdict
The fact that the Surface Laptop ships with a limited – sorry, “streamlined” – operating system and costs more than some previous Surface systems that come with full fat Windows 10 cannot go unnoticed – regardless of the free upgrade through this year. Unless Microsoft changes its tune come 2018, folks buying one of these with holiday gift money at the turn of the year would be wise to tack 50 bucks on top of whichever configuration they choose to get Windows 10 Pro.
While this switch will be free for any Surface Laptops bought in the education sector, that won’t help the Surface Laptop’s target audience come 2018: late high school and college students.
That said, the Surface Laptop’s incredible, potentially trendsetting design cannot go unnoticed either. Frankly, this is a laptop that appears to outclass the MacBook Air and 12-inch MacBook – and possibly even the 13-inch MacBook Pro – for hundreds less.
Save for a questionable platform versus pricing decision, the Surface Laptop has all the makings of yet another winning piece of hardware from Microsoft.
Have questions?
Get answers from Microsofts Cloud Solutions Partner!
Call us at: 856-745-9990 or visit: https://southjerseytechies.net/
South Jersey Techies, LL C is a full Managed Web and Technology Services Company providing IT Services, Website Design Services, Server Support, Network Consulting, Internet Phones, Cloud Solutions Provider and much more. Contact for More Information.
To read this article in its entirety click here.