RaaS has outgrown smaller targets and now threatens governments, NGOs, and SMBs.

It starts with a fast click on a link in a harmless-looking email. Then your PC slows to a crawl. A message suddenly pops up and takes over your screen. “Your files and hard drive have been locked by strong encryption. Pay us a fee in 12 hours, or we will delete everything.” Then a bright red clock begins counting down. No antivirus will save your machine. Pay the fee or lose everything.
You’re the latest victim of a ransomware attack. The scary thing is, you’re not alone. The ransomware market ballooned quickly, from a $400,000 US annual haul in 2012, to nearly $18 million in 2015. The average ransom—the sweet spot of affordability for individuals and SMBs—is about $300 dollars, often paid in cash vouchers or Bitcoin.
The ransomware market scaled up so quickly, claims a recent report by Imperva, due to the rise of ransomware-as-a-service, or RaaS. Here’s how it works:
- Ransomware authors are marketing on-demand versions of code, using traditional malware distributors in a classic affiliate model.
- The ransomware author collects the ransom and shares it with the distributor.
- Malware is distributed through spam email messages, malicious advertisements, and BlackHat SEO sites.
- According to the Imperva report, “in classical affiliate marketing, the larger cut goes to the possessor of the product. In RaaS … the ransomware author gets a small cut of the funds (5%-25%) while the rest goes to the distributor (affiliate).”
- Using the deep web, TOR, and Bitcoin, the report says, “this model, based on TOR and Bitcoins, is designed to keep the identity of the author and the distributor hidden from law enforcement agencies.”
Phishing in particular, is a highly effective tactic for malware distribution.
The well-worded email appears to come from a legitimate email address and domain name, and raises very few irregularities. The email comes with a demand for money for an arbitrary service, along with a link that purports to be an “overdue invoice.”
Click that link and open the file (which looks like a Word document), and you’ll become the latest victim of ransomware — that is, malware that encrypts your files and locks you out of your computer until you pay a ransom.
Phishing attacks have also helped ransomware move into the enterprise. In 2015 the medical records system at Hollywood Presbyterian Medical Center was attacked. The hospital paid $17,000 in Bitcoin to unlock the sensitive records. In early 2016 the Lincolnshire County Council was snagged by a phishing scheme and held up for 500 dollars.
To prevent your business from attack, make sure the IT department and communication team are in sync, keep your company’s security systems updated, and remind employees to use caution when clicking on email links from unknown addresses.
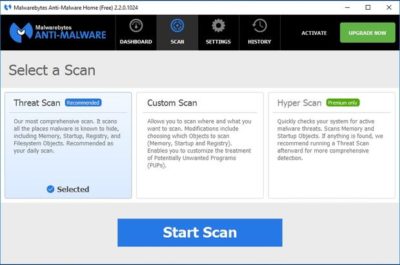
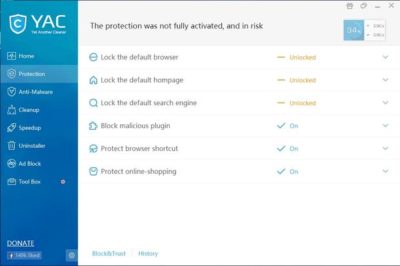
If you’ve been hacked, the ransomware rescue kit provides a suite of tools designed to help clean particularly pugnacious malware.
Businesses that suffer ransomware attacks face a tough choice. Paying the fee could restore access to mission-critical data, but there’s no guarantee the extortionists will honor the deal. And of course, paying a ransom provides incentive to hackers and validates the attack.
Have questions?
Get answers from Microsofts Cloud Solutions Partner!
Call us at: 856-745-9990 or visit: https://southjerseytechies.net/
South Jersey Techies, LL C is a full Managed Web and Technology Services Company providing IT Services, Website Design Services, Server Support, Network Consulting, Internet Phones, Cloud Solutions Provider and much more. Contact for More Information.