Don’t expect your money anytime soon, however.

DVD drives may be a thing of the past, but the past could pay you $10 via a proposed settlement from a class-action suit.
If you purchased a DVD-ROM, DVD-RW or combination drive between April, 2003 and December 31, 2008, a collection of DVD drive manufacturers have tentatively agreed to pay you $10 per drive, whether you purchased the drive as part of a PC or by itself. You’ll simply need to visit the claim site and testify (under penalty of perjury) that you indeed purchased those drives within the given time period, and live in one of the 23 states (plus the District of Columbia) covered by the suit. The deadline to file is July 1.
Why this matters: Though the optical drive market continues to decrease—“the physical disk format is somewhat obsolete in the era of content streaming,” IDC wrote last year—that wasn’t the case fourteen years ago, when virtually all software was distributed via DVD-ROM. Fortunately, the settlement site isn’t asking for proof of purchase yet, but it reserves the right to do so. Filing a claim can take literally seconds, but don’t hold your breath—you’ll probably receive compensation, but there’s no guarantee.
The wheels of justice turn slowly
Simply put, a group of 23 plaintiffs sued virtually every DVD drive manufacturer, alleging that they collectively conspired to keep drive prices higher than they normally would be, in violation of antitrust laws. Though the defendants denied they did anything wrong, several—Hitachi-LG, Panasonic, NEC, and Sony—settled and agreed to pay a collective total of $124.5 million into four separate settlement funds.
(Note that only DVD drives for PCs are covered; a DVD player, such as the one gathering dust in your living room, isn’t.)
If you do submit a claim, however, the chances of receiving your settlement soon are slim. That’s because seventeen more defendants, including various subsidiaries of BenQ, Philips, Samsung, TEAC, and Pioneer, have yet to settle, and the suit will continue until all of the claims are resolved.
“Because other defendants remain in this litigation, the plaintiffs are proposing that distribution of the settlement funds not occur at this time,” the settlement site reads. “This is to save the expenses associated with distribution.”
In fact, the settlement hearing to finally approve the Hitachi-LG-Panasonic-NEC-Sony agreement will be held on December 8. After that, payments may begin—which means that you’ll probably receive your $10 or less a year from now. Yes, less: Payments will be “up to” $10 per drive, according to the claims site.
You should probably treat the settlement like one of those “print out your own rebate” slips from the turn of the century. Even under the best of circumstances, chances are you’ll have totally forgotten about your $10 windfall by the time the check arrives.
Have questions?
Get answers from Microsofts Cloud Solutions Partner!
Call us at: 856-745-9990 or visit: https://southjerseytechies.net/
South Jersey Techies, LL C is a full Managed Web and Technology Services Company providing IT Services, Website Design Services, Server Support, Network Consulting, Internet Phones, Cloud Solutions Provider and much more. Contact for More Information.
To read this article in its entirety click here.










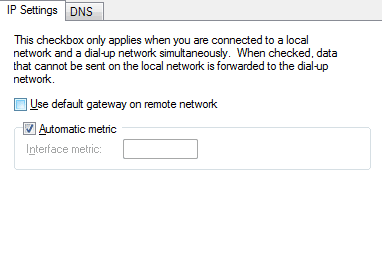 Now you will be able to browse the internet through the VPN on Windows 10.
Now you will be able to browse the internet through the VPN on Windows 10.