In a change to its longstanding support policy, Microsoft says PCs based on new CPU architectures, including Intel’s Skylake chips, will require Windows 10. A list of preferred systems will support older Windows versions on new hardware, but only for 18 months.
Enterprise customers are still the bulwark of Microsoft’s Windows business, in both the client and server segments.
Historically, those customers have also been among the most conservative, lagging years behind the latest releases of an operating system release. Those practices have been encouraged by Microsoft’s support lifecycle, which offers a generous ten years of support for each Windows release.
Effective today, that policy is changing in a subtle but significant way, with the addition of new hardware requirements for support of pre-Windows 10 releases. The company’s also publishing a preferred list of systems that will receive special attention for updates and support.
Yes, Windows 7 (currently in the Extended support phase) will continue to receive updates until January 14, 2020, and Windows 8.1 will be supported until January 10, 2023. But in a series of “clarifications” to its support policy today, the company announced that support for those older Windows versions will be available only for “previous generations of silicon.”
Going forward, as new silicon generations are introduced, they will require the latest Windows platform at that time for support… Windows 10 will be the only supported Windows platform on Intel’s upcoming “Kaby Lake” silicon, Qualcomm’s upcoming “8996” silicon, and AMD’s upcoming “Bristol Ridge” silicon.
The policy will be phased in beginning with systems based on Intel’s new 6th-generation CPUs (code-named Skylake), which debuted a few months ago. New consumer-based Skylake devices must run Windows 10 to be supported.
For enterprise customers that want to buy “future proof” new hardware based on Skylake processors running older Windows versions, Microsoft will publish “a list of specific new Skylake devices we will support to run Windows 7 and Windows 8.1.” That support will run for a period 18 months, until July 17, 2017, after which those enterprise customers will be expected to upgrade to Windows 10.
Examples of systems that will be on the initial release of the list include Dell’s Latitude 12, Latitude 13 7000 Ultrabook, and XPS 13; HP’s EliteBook Folio, EliteBook 1040 G3; and Lenovo’s ThinkPad T460s, X1 Carbon, and P70 models.
The list will continue to be updated, Microsoft says.
Any machine that earns a place on the elite enterprise support list will get very special treatment indeed, with the idea being to reassure corporate customers that these models are especially likely to perform well on Windows 10 in the new era of continuous updates:
For the listed systems, along with our OEM partners, we will perform special testing to help future proof customers’ investments, ensure regular validation of Windows Updates with the intent of reducing potential regressions including security concerns, and ensure all drivers will be on Windows Update with published BIOS/UEFI upgrading tools, which will help unlock the security and power management benefits of Windows 10 once the systems are upgraded.
These models also get special treatment for enterprises that are still planning their Windows 10 migration, with an 18-month grace period where the older OS versions are fully supported.
Through July 17, 2017, Skylake devices on the supported list will also be supported with Windows 7 and 8.1. During the 18-month support period, these systems should be upgraded to Windows 10 to continue receiving support after the period ends. After July 2017, the most critical Windows 7 and Windows 8.1 security updates will be addressed for these configurations, and will be released if the update does not risk the reliability or compatibility of the Windows 7/8.1 platform on other devices.
Of course, enterprise customers who want to stick with earlier Windows versions beyond that mid-2017 deadline have lots and lots of options, based on current generations of Intel processors such as the Broadwell and Haswell lines. Those systems, which are based on what Microsoft calls “downlevel silicon,” will continue to be fully supported for pre-Windows 10 operating systems.
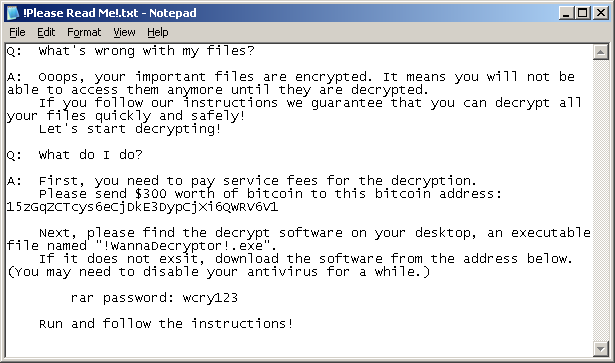
In today’s blog post, Microsoft says it’s seeing “unprecedented demand from our enterprise customers” in Windows 10. Enterprise customers are especially interested in new Windows 10 security features like Credential Guard, which uses hardware virtualization to safeguard credentials from attack.
Windows 8-era enhancements like Secure Boot, which protects systems from being compromised by rootkits and bootkits, also require new hardware.
Not surprisingly, today’s announcement contains the usual cheery statements from Microsoft’s three biggest hardware partners: Dell, HP, and Lenovo. All three companies compete aggressively in the low-margin consumer market, where virtually all new systems will run Windows 10. But enterprises will pay premium prices for the improvements in battery life and security in Skylake-based mobile systems, making this the most attractive segment to target.
Have questions?
Get help from IT Experts/Microsofts Cloud Solutions Partner
Call us at: 856-745-9990 or visit: https://southjerseytechies.net/
South Jersey Techies, LL C is a full Managed Web and Technology Services Company providing IT Services, Website Design Services, Server Support, Network Consulting, Internet Phones, Cloud Solutions Provider and much more. Contact for More Information.
To read this article in its entirety click here.