What Is Rogue Anti-virus Software?
It is almost unheard of in this day and age to be online without using anti-spyware and anti-virus software to safeguard your computer against viruses and other malicious code. It’s not surprising to see the prevalence of rogue anti-virus software.
Also called scareware, or rogue security software, or smitfraud, this type of software is also most commonly defined as malware—it is designed specifically to damage or disrupt your computer system. In this case, not only is the software going to disrupt your system, it’s going to try and trick you into making an unsecure credit card purchase.
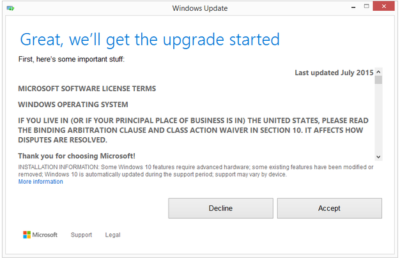
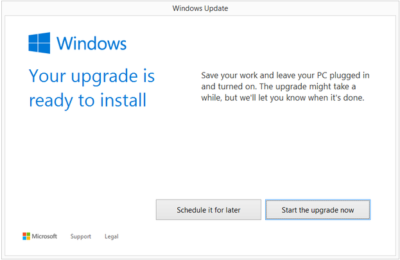
Rogue anti-virus programs usually appears in the form of a fake Windows warning on your computer system that reads something like, you have a specific number of viruses on your computer (usually in the hundreds) and that this software has detected those viruses. To get rid of these viruses, you’re prompted to buy the full-version of the antivirus software (which is really rogue antivirus software).The good news is that you probably do not have a computer that is infested with hundreds of viruses as the rouge software claims. The bad news is that the rogue antivirus software itself is on your computer and you must remove it. Removal is hindered as rouge software can lock the control panel and the the Add/Remove Programs function to prevent you from removing it easily.
Other things that may be disrupted by the rogue software include being unable to visit reputable and valid anti-virus and malware Web sites, being able to install legitimate antivirus software and also being unable to access your desktop.
The rogue software wants to stop users from removing the program and proceeding with the purchase instead. It’s important to remember that by purchasing the “claimed full version to remove the viruses” you will be submitting your personal information to unscrupulous persons and may also end up being a victim of credit card or identity theft.
Common names of rogue antivirus software include; AntiVirus (2007, 2008, and 2009), MS-Antispyware, XP AntiVirus (2007, 2008, and 2009), Home Antivirus 2009, SpyWareGuard, Malware Cleaner, Extra Antivirus, AV AntiSpyware, SpywareProtect2009, WinPC Defender as well as many other names.
How Does a Computer Get Infected with Rogue Antivirus Programs?
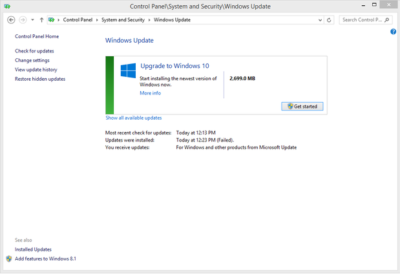
The reason these rogue anti-virus programs are successful (for the malicious coders) is because the warning screens very closely resemble legitimate Windows warning screens, plus the rouge software program names closely resemble or sound like legitimate antivirus programs.When you load an infected Web site you might see a warning screen pop up and think that it is a legitimate Windows warning. Users unknowingly are tricked into downloading the software because they believe the warning to be a legitimate Windows messages.
You might also be on a Web site trying to view a video and a screen may pop-up telling you that you need to download a codec to view the file. The window prompting you to download the codec looks legitimate, however you are not going to download a codec—instead you will receive one of the many rogue antivirus software programs.
In April of this year, it was also reported that systems that had been previously infected with Conficker, found this worm had began installing rogue antivirus programs on infected machines. In the early cases this turned out to be a rogue application called SpywareProtect2009. Kaspersky researchers reported this was a typical rogue program that offered to clean the computer for $49.95.
Lastly, if you use file sharing networks you also risk downloading a rogue antivirus as it can be easily hidden inside a legitimate program—that you may or may not be legitimately downloading.
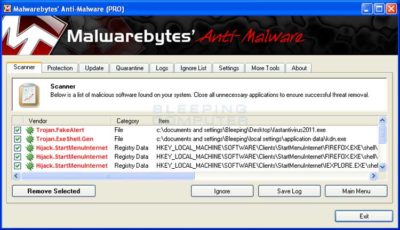
How to Spot Rogue Antivirus WarningsFor the most part, you need to look at the windows that are popping up and the name of the program being shown. If you know the program name of the antivirus and spyware software you use, then seeing a different name in the warning window is the first clue. Also, Windows itself doesn’t warn you of a virus. Legitimate warnings on your system would come from the anti-virus program you have installed, not a random Windows operating system style pop-up window. A great resource for learning how to spot these malicious programs through fake warning messages can be found on bleepingcomputer.com. This page lists the text of some of the more common false warning screens, including the following:
Malware Cleaner: Trojan detected! A piece of malicious code was found in your system that can replicate itself if no action is taken. Click here to have your system cleaned by Malware Cleaner.
AV AntiSpyware: Spyware Alert! Your computer is infected with spyware. It could damage your critical files or expose your private data on the Internet. Click here to register your copy of AV AntiSpyware and remove spyware threats from your PC.
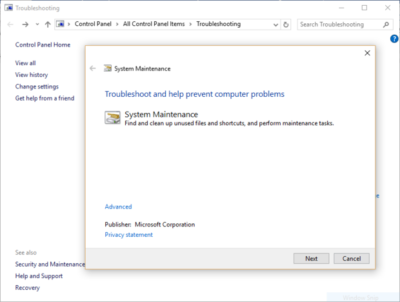
How Do I Get Rid of Rogue Antivirus Programs?It can be a difficult task to get rogue anti-virus programs off your computer. To complicate the matter, there are many variations of this malicious program and not all variants can be removed in the same way. This is not something that novice computer users may be able to deal with on their own.
Also, due to the popularity of these infections and people searching for answers on how to remove the program a number of scam programs also exist that lead users to believe it will remove the infection. Yes, these programs that claim to rid your system of Antivirus 2009 (or whichever variant you have been infected with) will scan your system and then prompt you for a credit card number so you can download a full version to remove the infection. Sound familiar? It should. This is a vicious cycle that users can unwittingly become trapped in.
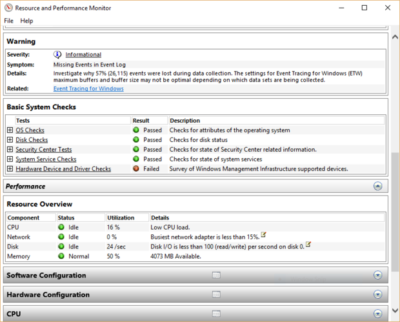
Still, the good news is that in many instances you can get rid of the rouge antivirus program without wiping and formatting your hard drive. If you are already infected and you cannot access legitimate security related Web sites, you will need to download the following programs from a second computer and burn them to CD to run on the infected computer.
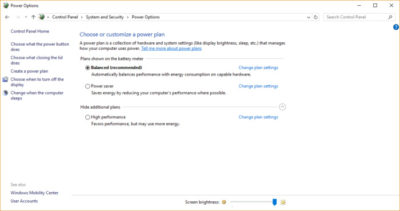
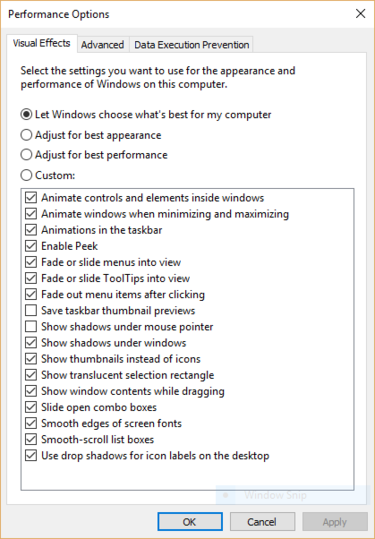
WARNING: Before running any of the following programs, you should turn off System Restore (you won’t be able to use System Restore as this deletes all restore points). If you don’t turn it off, the programs may not be able to access those system files to clean them. If you are infected the System Restore is not going to return you to an earlier uninfected date anyway. You can turn it back on after you have successfully removed the rouge antivirus program.
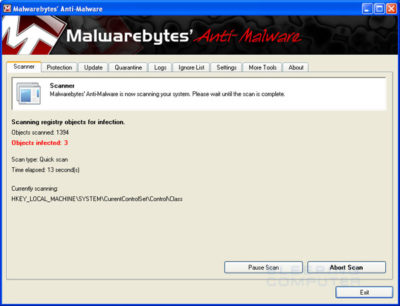
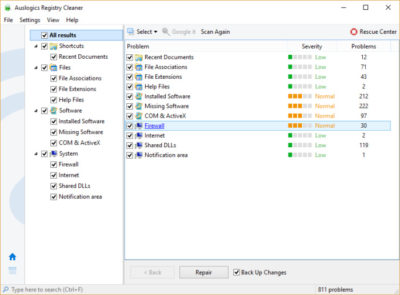
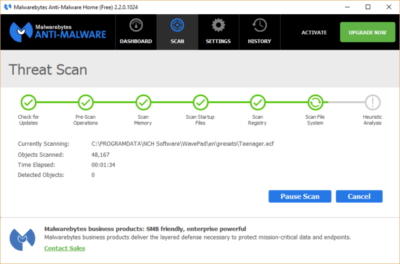
The quickest way, and first thing to try is to download Malwarebytes Anti-Malware to get rid of the rogue antivirus. On it’s own this will usually rid your computer of the problem. If Malwarebytes didn’t have the desired results, or you simply want to do a total and complete system clean, you will want to use a combination of CCleaner, Malwarebytes, Asquared, and SpyBot Search and Destroy. These programs all offer freeware versions.
NOTE: In some cases, the rogue anti-virus may block one or more of these legitimate programs. If this is the case, you will need to open the folder where you installed the program on your hard drive and rename the executable file (.exe) to anything other than the program’s name. (e.g. rename mbam.exe to aaa.exe).
Once you have run all the programs, be sure to go back and run CCleaner a final time to get rid of dead registry links from having the rouge antivirus removed. Continue to run the registry option of this program until no problems are found.
Here are additional removal resources:
bleepingcomputer.com: How to remove Extra Antivirus
bleepingcomputer.com: How to uninstall and remove AV AntiSpyware
bleepingcomputer.com: How to uninstall and remove WiniBlueSoft
bleepingcomputer.com: How to uninstall and remove HomeAntivirus 2009
bleepingcomputer.com: How to uninstall and remove Antivirus 2009 (Antivirus 09)
bleepingcomputer.com: How to uninstall and remove PAntispyware09
bleepingcomputer.com: How to uninstall and remove Virus Sweeper
bleepingcomputer.com: How to uninstall and remove WinPC Antivirus
Kaspersky Technical Support and Knowledge Base: How to disinfect rogue spyware
DID YOU KNOW…
In December 2008 it was reported that a Google sponsored link pointed to a malicious Web site where users were redirected to a spoofed CNET Download.com site with offers to download a “spyware free” copy of Winrar. This file included the rogue antivirus program “AntiSpyware2008” (Source)
To read the original article in it’s entirety Click Here