![]()
Even a novice Word user can display page numbers in a document’s header of footer. The process is fundamental. Advancing beyond the basics is easier than you might think, and you might be surprised how many things you can do with a header or footer! In this article, you’ll find eight tips that will move you from basic user to advanced, at least with headers and footers.
1. Display page numbers in shapes
Most documents over a few pages display a page number in the header of footer. If the document warrants a bit of visual appeal, you can display that number in an interesting and colorful shape. First, add the shape to the header using an easy-to-use built in gallery. Next, use the header’s current position property to add the number.
To add the shape, do the following:
- Open the footer by double-clicking the footer area. In Word 2003, choose Header and Footer from the View menu.
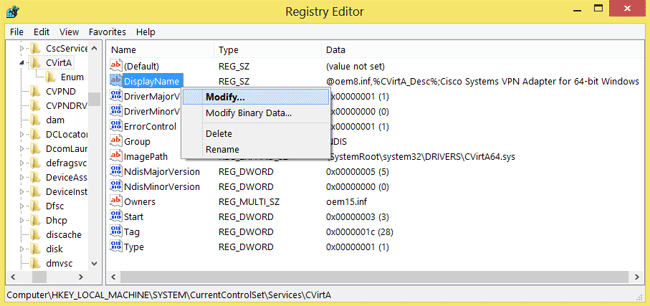
- While in the header, click the Insert tab. In the Illustrations group, click Shapes and choose one, such as the diamond shape in the Flowchart section (Figure A). In Word 2003, use the Drawing toolbar to access shapes.
Figure A

- Click inside the footer and drag to create the shape. It’s okay if the shape extends beyond the footer border a bit.
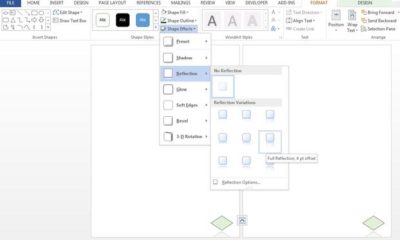
- With the shape inserted, use the contextual Format tab to format the shape. I used the Shape Fill options to change the color to lettuce green; I used the Shape Outline drop-down to change the outline to dark green; I used the Shape Effects Reflection option to add a full reflection (Figure B) that fades off the bottom edge (which might not be possible to print but works fine for electronic viewing). In Word 2003, choose AutoShape from the Format menu (with the shape selected).
Figure B
With the shape inserted and formatted, add the page number as follows:
- Right-click the shape and choose Add Text from the resulting submenu. In Word 2003, use the Header and Footer contextual toolbar to insert the page number, and then format as you normally would.
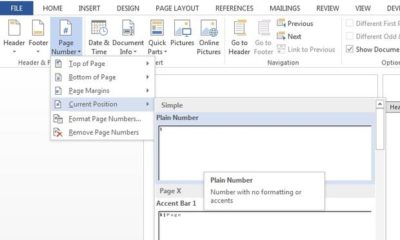
- Click the contextual Design tab. In the Header & Footer group, click Page Number.
- Choose Current Position from the drop-down.
- Choose Plain Number (the first option) from the gallery (Figure C).
Figure C
- Select the number and format it. I applied black font color (Figure D).
Figure D

This simple example shows you how to display the page number in a shape. It’s up to you to determine whether doing so is appropriate for your document.
2. Insert a graphic
A header is a good place to display your organization’s logo or some other branding graphic. To do so, open the header or footer as you normally would and then do the following:
- With the document in edit mode, click the Insert tab. In Word 2003, choose Picture | From File from the Insert menu, and then skip to step 3.
- In the Illustrations group, click Picture.
- Use the Insert Picture dialog to locate the file
- Select the file, and then click Insert
You probably didn’t realize how easy that would be! While graphics in the header and footer might sound like a great idea, use them sparingly.
3. Use header graphic as a page tab
You can use the header or footer to display a graphic on every page, but you don’t have to leave it in the header or footer. For instance, you might want to use a graphic as a page tab. To do so, insert the graphic as you normally would (see tip 2). Then, drag it out of the header or footer area as shown in Figure E. If the graphic won’t move, click the Layout Options icon and choose a text wrapping option. The Layout Options icon is new to 2013. In earlier versions, you’ll find these options on the contextual Format tab. You might want to rotate the graphic as well.
Figure E

4. Use sections
A large document might need to change information in the header or footer as the document evolves. The way to implement this requirement is to use section breaks. Simply click inside the document (not inside the header or footer) where you want the new section to begin. Click the Page Layout tab, click Breaks in the Page Setup group, and then choose the best break type for your document. Return to the header or footer of the new section and make the necessary changes. In Word 2003, breaks are on the Insert menu.
For a header that doesn’t repeat information from the previous section, click the Link to Previous option in the Navigation group on the contextual Design tab. Doing so breaks the connection between the two sections. Figure F shows the toggle option linked and not linked. When sections are linked, the option has a dark background and Word displays the Same as Previous tab to the right. When the link is broken, the option has no background and the tab is gone. In Word 2003, this option is on the Header and Footer toolbar (and available only if there’s more than one section).
Figure F

You must break the link between headers and footers separately.
5. Display custom info
The header or footer area is a great place to display custom information about the document or author using fields. To do so, open the document’s header or footer. Then, position the cursor and do the following:
- Click the Insert tab. In Word 2003, choose Field from the Insert menu and skip to step 4.
- In the Text group, click the Quick Parts option.
- From the drop-down, choose Field.
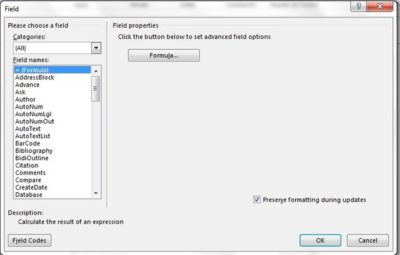
- Using the resulting dialog (Figure G), choose a field, such as Author. Set properties, if necessary, and click OK. (You could also use AutoText or Document Property.)
Figure G
6. Gallery page number options replace existing header or footer
Be careful when using the Page Number option to display page numbers in the header or footer. If you’ve already created a header or footer, and you add the page number last, use the Current Position option. Other options from the gallery will replace the existing header or footer. (Galleries aren’t available in Word 2003.)
7. Modify the style
Word applies the Header and Footer style to header and footer text, respectively. Both styles are based on Normal. The easiest way to change the appearance of the text for either is to modify the appropriate style. Doing so will impact the entire document, so don’t change the style if you want to change the format for a single section.
8. Reference a content control
Sometimes, you want to repeat information from the body of the document in the header or footer. In later versions of Word, using content controls, this is easily done. First, you add a content control and create a custom style for it. To the header, you add a StyleRef field that references the style you applied to the content control. In this way, you can easily display the contents of the content control in the header. Let’s work through a simple example:
- Position the cursor where you want to insert the content control.
- Click the Developer tab and then click Rich Text Content Control in the Controls group.
- Click Properties in the same group and enter a meaningful name, such as ccName . The cc prefix identifies the object as a content control and Name describes its content.
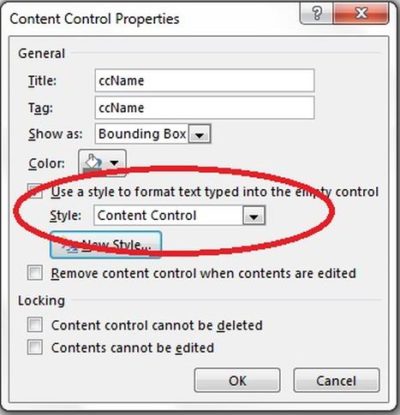
- Check the Use a style to format text typed into the empty control option. Don’t worry about what’s in the Style control at this point.
- Click New Style.
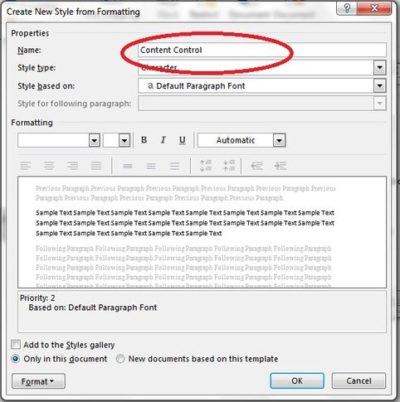
- Name the new style appropriately, such as Content Control (Figure H). You can change the Style based on setting, but don’t for this example. In this way, you can see how easy it is to set this technique up without making a lot of unnecessary changes. It’s the same style used for the body of the document; it just has a different name.
Figure H
- Click OK, and Word updates the Style control to reflect the new style you just created (Figure I).
Figure I
- Click OK.
- Open the header and position the cursor where you want to display the contents of the content control you just added.
- Click the Insert tab.
- In the Text group, click Quick Parts, and choose Field from the drop-down list.
- In the resulting dialog, choose StyleRef from the Field names list.
- Choose Content Control from the Style name list
- Click OK.
- Double-click the content control to close the header.
Enter text into the content control, and the field in the header will update accordingly. Although this technique has a lot of steps, it isn’t difficult to implement.
Have questions?
Get help from IT Experts/Microsofts Cloud Solutions Partner
Call us at: 856-745-9990 or visit: https://southjerseytechies.net/
South Jersey Techies, LLC is a full Managed Web and Technology Services Company providing IT Services, Website Design Services, Server Support, Network Consulting, Internet Phones, Cloud Solutions Provider and much more. Contact for More Information.
To read this article in its entirety click here.