Enhanced anti-spoofing safeguards are rolling out for Office 365.
Microsoft services like OneDrive for Business, SharePoint Online, and Microsoft Teams are closely guarded by ATP (Advanced Threat Protection). Besides, there are numerous feature updates available in Office 365 threat protection service to address the evolution and advances in the threat landscape. The addition of enhanced Anti-Spoofing capability in Office ATP for protecting against spoofed emails from external domains further strengthens this security framework.
Anti-spoofing in Office 365 Advanced Threat Protection
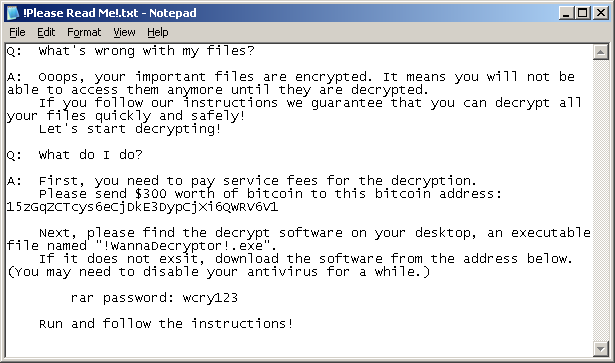
The newest anti-spoof features help protect organizations from external domain spoof. Office 365 recognizes emails from external domains having proper SPF, DMARC, and DKIM authentication settings as legitimate/authentic and therefore allow them to pass authentication, uninterrupted.
This normal process is however challenged when external domains do not have these settings properly configured. Without enforcement of these settings, domains show a high likelihood of being manipulated and maliciously spoofed, leaving customers vulnerable to phishing or spam attacks. The new external domain anti-spoofing capabilities help detect and block emails from external domains that do not have the following features,
- Correct authentication configuration
- An email infrastructure source with an unknown history
How does it work?
A newly enhanced filter in ATP first checks if the email from external domains, passes SPF, DKIM, and DMARC test. If not, the filter thoroughly checks for historical sending patterns of that domain and associated infrastructure. If any suspicious behavior is noted, ATP assumes the sender does not bear a good reputation and as such, proceeds to junk the message.
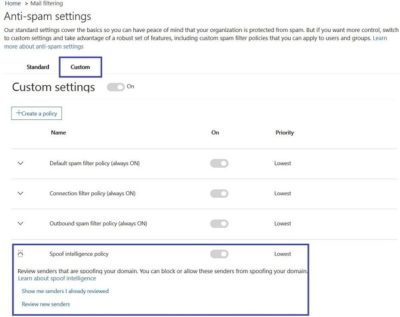
Also, a feature worth noticing about Anti-spoofing – The filter constantly evolves and enhances itself based on mail flow patterns it observes. ATP subscribers can access the spoof intelligence report in their Antispam Policy and take necessary actions if required.